-
Rickshaw in Karachi
Abstract Alberta Bald Eagle Beach Butterfly Cameron Diaz Cancer Wing Hallway Circus Coloring Drawing Flowers Flower Vase Giraffe Horses House Jinnah Karachi Lincoln Lion Niagara Falls Paint Painting Pakistan Panorama Parrot Pencil Photograph Rainbow Rickshaw Smiling Snow Sun Sunflower Sunnybrook Sunset Tree Tulips Yacht York University

-
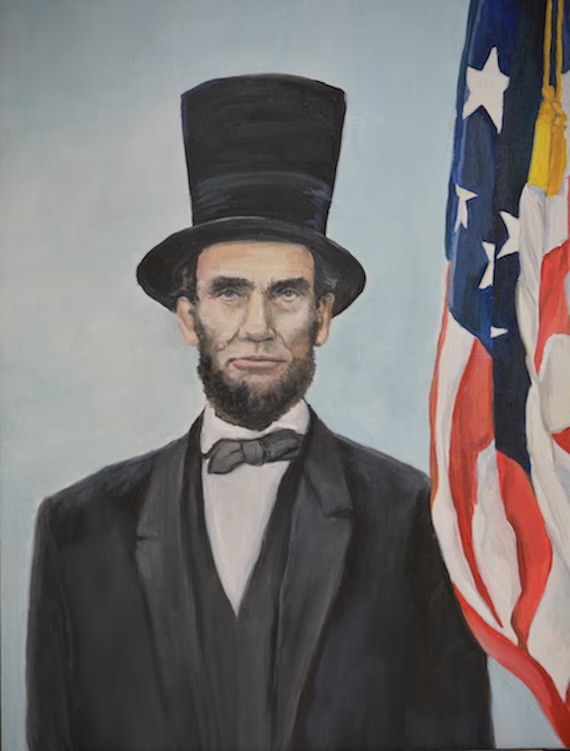
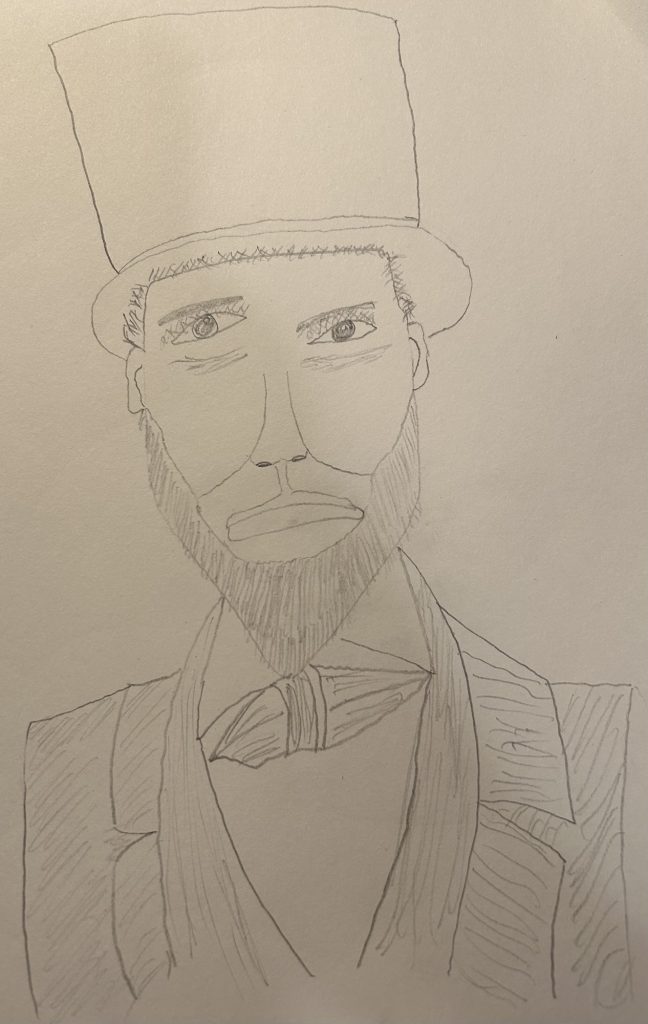
Abraham Lincoln
Abstract Alberta Bald Eagle Beach Butterfly Cameron Diaz Cancer Wing Hallway Circus Coloring Drawing Flowers Flower Vase Giraffe Horses House Jinnah Karachi Lincoln Lion Niagara Falls Paint Painting Pakistan Panorama Parrot Pencil Photograph Rainbow Rickshaw Smiling Snow Sun Sunflower Sunnybrook Sunset Tree Tulips Yacht York University
-
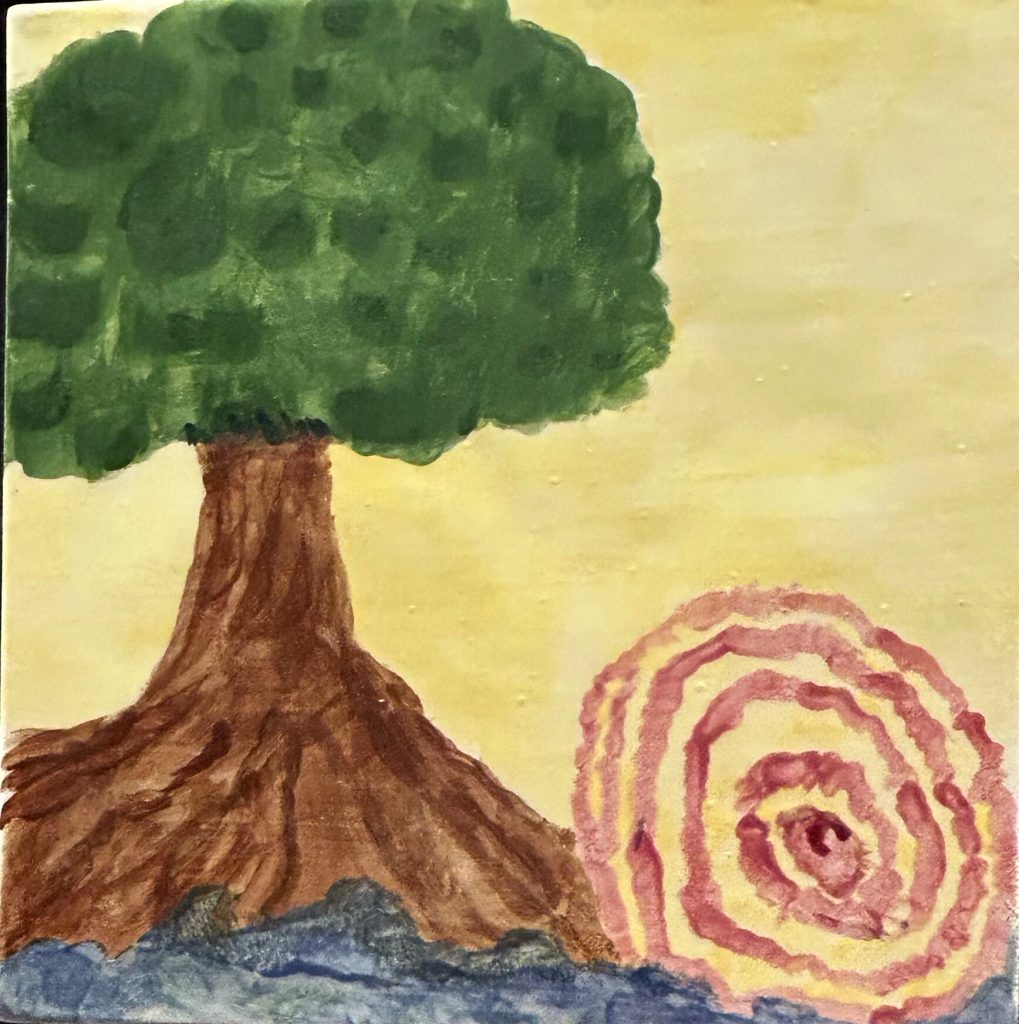
Tree web
Abstract Alberta Bald Eagle Beach Butterfly Cameron Diaz Cancer Wing Hallway Circus Coloring Drawing Flowers Flower Vase Giraffe Horses House Jinnah Karachi Lincoln Lion Niagara Falls Paint Painting Pakistan Panorama Parrot Pencil Photograph Rainbow Rickshaw Smiling Snow Sun Sunflower Sunnybrook Sunset Tree Tulips Yacht York University
-
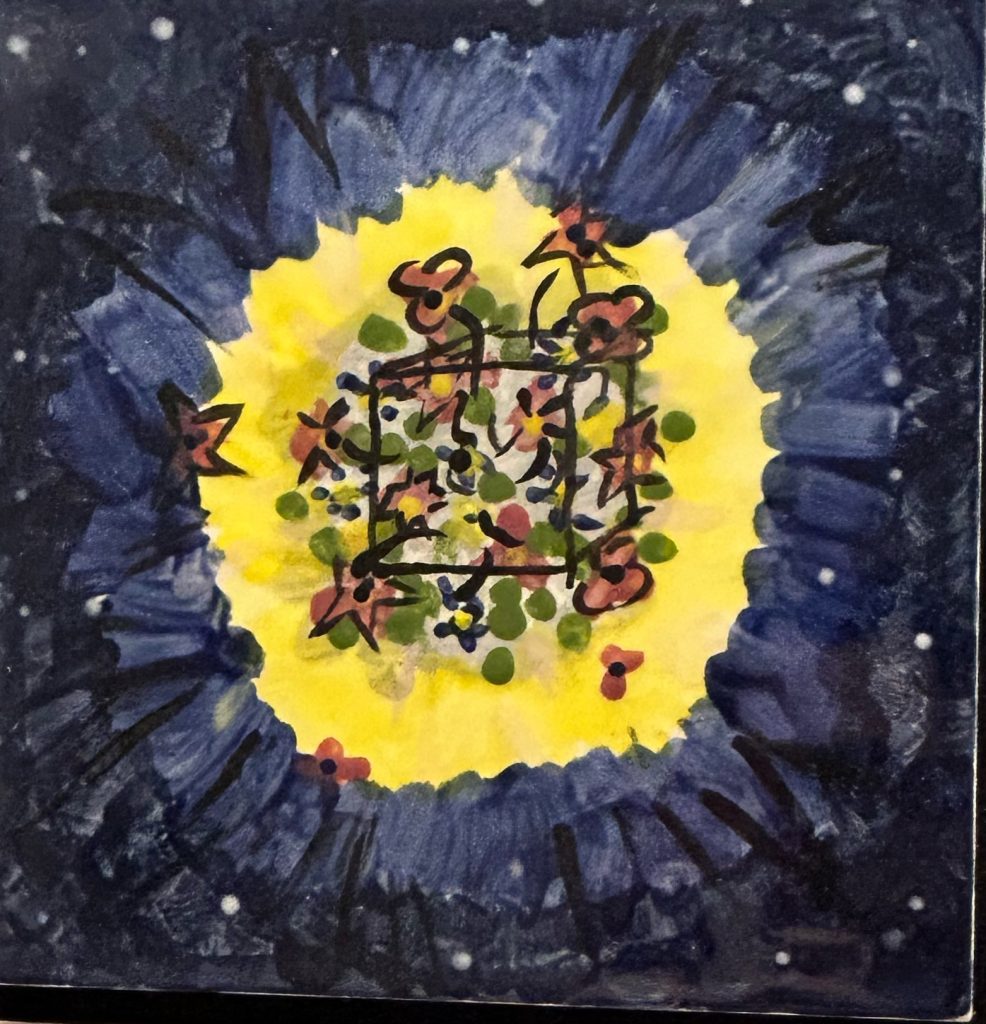
Abstract
Abstract Alberta Bald Eagle Beach Butterfly Cameron Diaz Cancer Wing Hallway Circus Coloring Drawing Flowers Flower Vase Giraffe Horses House Jinnah Karachi Lincoln Lion Niagara Falls Paint Painting Pakistan Panorama Parrot Pencil Photograph Rainbow Rickshaw Smiling Snow Sun Sunflower Sunnybrook Sunset Tree Tulips Yacht York University
-
Come hold my hand
Abstract Alberta Bald Eagle Beach Butterfly Cameron Diaz Cancer Wing Hallway Circus Coloring Drawing Flowers Flower Vase Giraffe Horses House Jinnah Karachi Lincoln Lion Niagara Falls Paint Painting Pakistan Panorama Parrot Pencil Photograph Rainbow Rickshaw Smiling Snow Sun Sunflower Sunnybrook Sunset Tree Tulips Yacht York University

-
Sun Smiling With Rays
Abstract Alberta Bald Eagle Beach Butterfly Cameron Diaz Cancer Wing Hallway Circus Coloring Drawing Flowers Flower Vase Giraffe Horses House Jinnah Karachi Lincoln Lion Niagara Falls Paint Painting Pakistan Panorama Parrot Pencil Photograph Rainbow Rickshaw Smiling Snow Sun Sunflower Sunnybrook Sunset Tree Tulips Yacht York University

-
Let it snow
Abstract Alberta Bald Eagle Beach Butterfly Cameron Diaz Cancer Wing Hallway Circus Coloring Drawing Flowers Flower Vase Giraffe Horses House Jinnah Karachi Lincoln Lion Niagara Falls Paint Painting Pakistan Panorama Parrot Pencil Photograph Rainbow Rickshaw Smiling Snow Sun Sunflower Sunnybrook Sunset Tree Tulips Yacht York University

-
Panorama View
Abstract Alberta Bald Eagle Beach Butterfly Cameron Diaz Cancer Wing Hallway Circus Coloring Drawing Flowers Flower Vase Giraffe Horses House Jinnah Karachi Lincoln Lion Niagara Falls Paint Painting Pakistan Panorama Parrot Pencil Photograph Rainbow Rickshaw Smiling Snow Sun Sunflower Sunnybrook Sunset Tree Tulips Yacht York University

-
York University
Abstract Alberta Bald Eagle Beach Butterfly Cameron Diaz Cancer Wing Hallway Circus Coloring Drawing Flowers Flower Vase Giraffe Horses House Jinnah Karachi Lincoln Lion Niagara Falls Paint Painting Pakistan Panorama Parrot Pencil Photograph Rainbow Rickshaw Smiling Snow Sun Sunflower Sunnybrook Sunset Tree Tulips Yacht York University

-
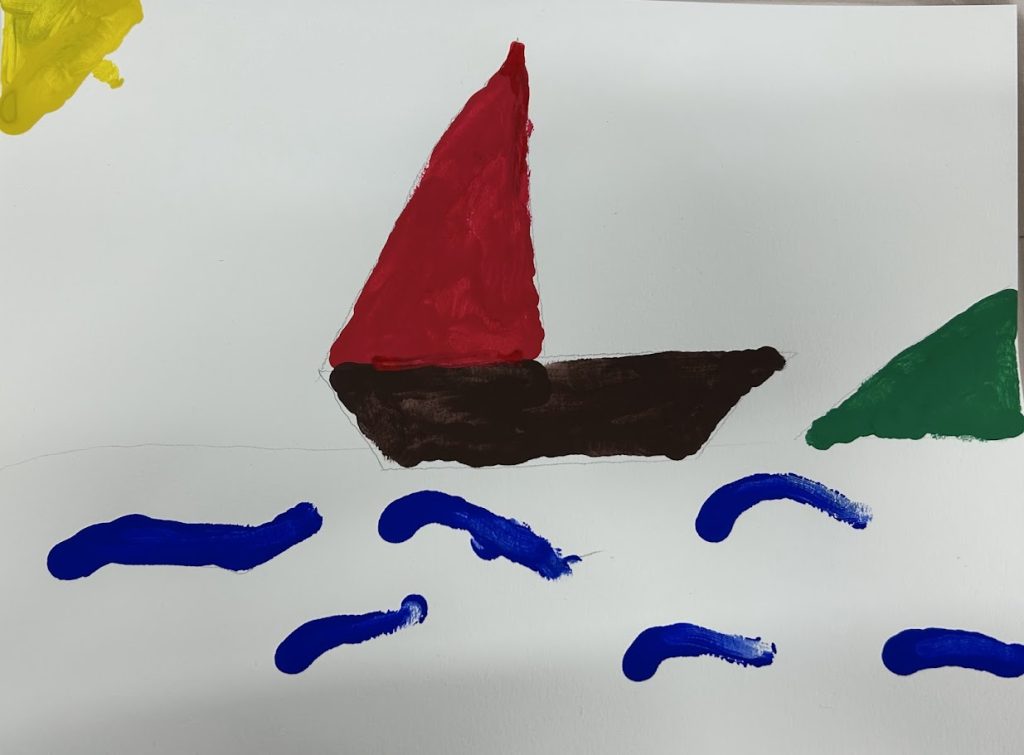
Yacht
Abstract Alberta Bald Eagle Beach Butterfly Cameron Diaz Cancer Wing Hallway Circus Coloring Drawing Flowers Flower Vase Giraffe Horses House Jinnah Karachi Lincoln Lion Niagara Falls Paint Painting Pakistan Panorama Parrot Pencil Photograph Rainbow Rickshaw Smiling Snow Sun Sunflower Sunnybrook Sunset Tree Tulips Yacht York University